Integrate with GitHub Enterprise Cloud
Support level: Community
What is GitHub Enterprise Cloud
GitHub Enterprise Cloud is a plan for large businesses or teams who collaborate on GitHub.com.
-- https://docs.github.com/en/enterprise-cloud@latest/get-started/learning-about-github/githubs-plans
This guide configures SAML SSO for a GitHub Enterprise Cloud organization.
For GitHub Enterprise Cloud with Enterprise Managed Users, see the GitHub Enterprise EMU integration guide.
Preparation
The following placeholders are used in this guide:
github.com/orgs/foois your GitHub organization, wherefoois the name of your organization.authentik.companyis the FQDN of the authentik installation.
This documentation lists only the settings that you need to change from their default values. Be aware that any changes other than those explicitly mentioned in this guide could cause issues accessing your application.
authentik configuration
To support the integration of GitHub Enterprise Cloud with authentik, you need to create an application/provider pair in authentik.
Create an application and provider in authentik
-
Log in to authentik as an administrator and open the authentik Admin interface.
-
Navigate to Applications > Applications and click Create with Provider to create an application and provider pair. (Alternatively you can first create a provider separately, then create the application and connect it with the provider.)
- Application: provide a descriptive name, an optional group for the type of application, the policy engine mode, and optional UI settings.
- Choose a Provider type: select SAML Provider as the provider type.
- Configure the Provider: provide a name (or accept the auto-provided name), the authorization flow to use for this provider, and the following required configurations.
- Set ACS URL to
https://github.com/orgs/foo/saml/consume. - Set Audience to
https://github.com/orgs/foo. - Set Issuer to
https://github.com/orgs/foo. - Set Service Provider Binding to
Post. - Under Advanced protocol settings, select an available Signing certificate. Download this certificate because it is required later.
- Set ACS URL to
- Configure Bindings (optional): you can create a binding (policy, group, or user) to manage the listing and access to applications on a user's My applications page.
-
Click Submit to save the new application and provider.
GitHub configuration
- Log in to GitHub as an organization owner.
- Navigate to your organization at
https://github.com/foo. - Click Settings.
- In the left sidebar, under Security, click Authentication security.
- Under SAML single sign-on, select Enable SAML authentication.
- Configure the following settings:
- Sign on URL: enter the SSO URL (Redirect) from the SAML provider that you created in authentik.
- Issuer: enter the Issuer that you configured in authentik.
- Public certificate: paste the full signing certificate that you downloaded from authentik.
- Signature method and Digest method: select the methods that match the authentik SAML provider settings.
- Click Test SAML configuration.
- After the test succeeds, click Save.
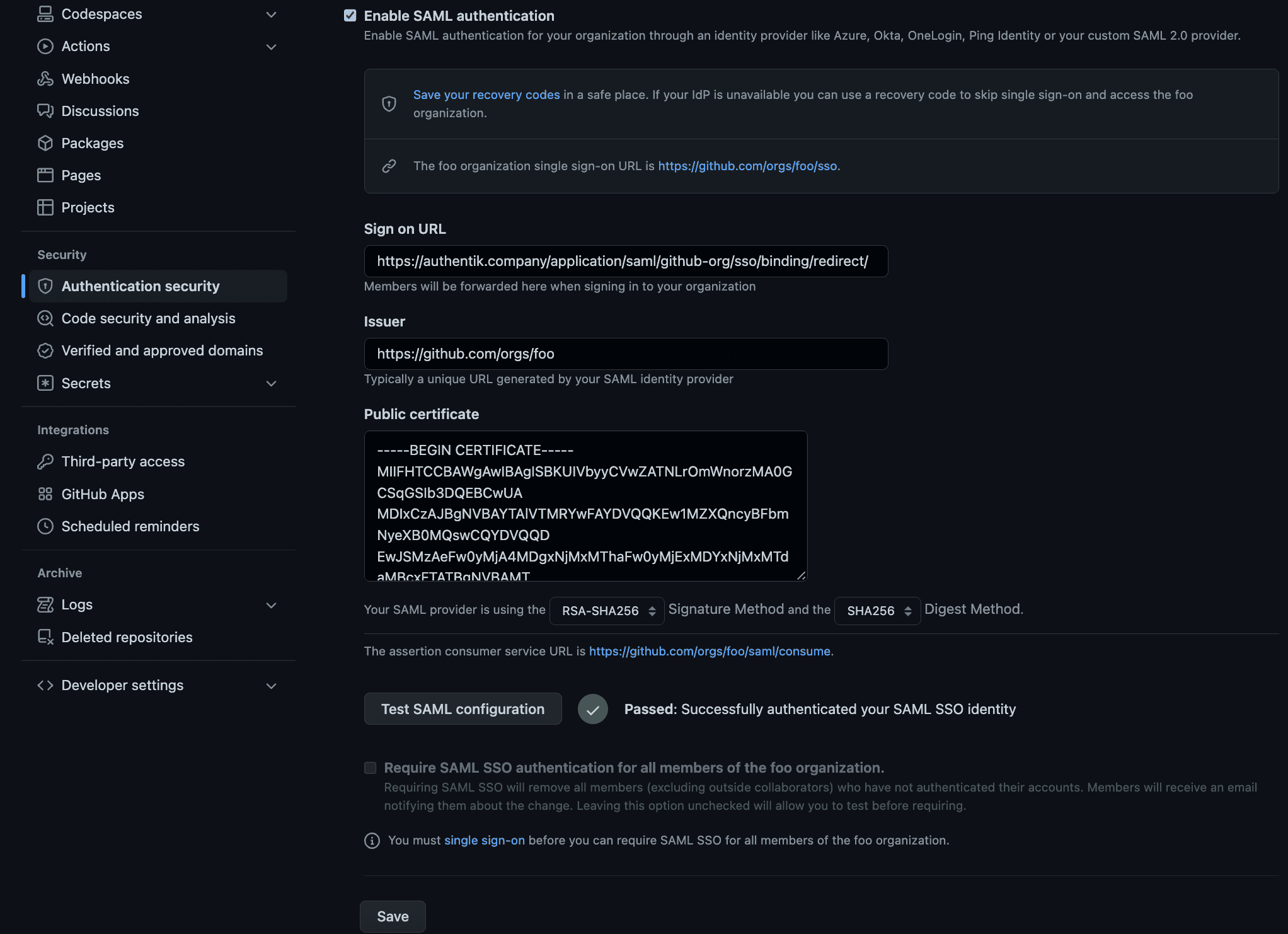
This enables SAML as an authentication option. To require SAML for all organization members, visit https://github.com/orgs/foo/sso, sign in with SAML, then return to Authentication security and select Require SAML SSO authentication for all members of the foo organization.
Configuration verification
To confirm that authentik is properly configured with GitHub Enterprise Cloud, log out of GitHub and then access a resource in the organization. GitHub should prompt you to authenticate with SAML through authentik.